Artificial intelligence fakes in the adult content space: what you’re really facing
Explicit deepfakes and strip images remain now cheap to produce, hard to trace, while being devastatingly credible upon first glance. This risk isn’t theoretical: AI-powered clothing removal tools and online nude generator systems are being employed for harassment, extortion, along with reputational damage on scale.
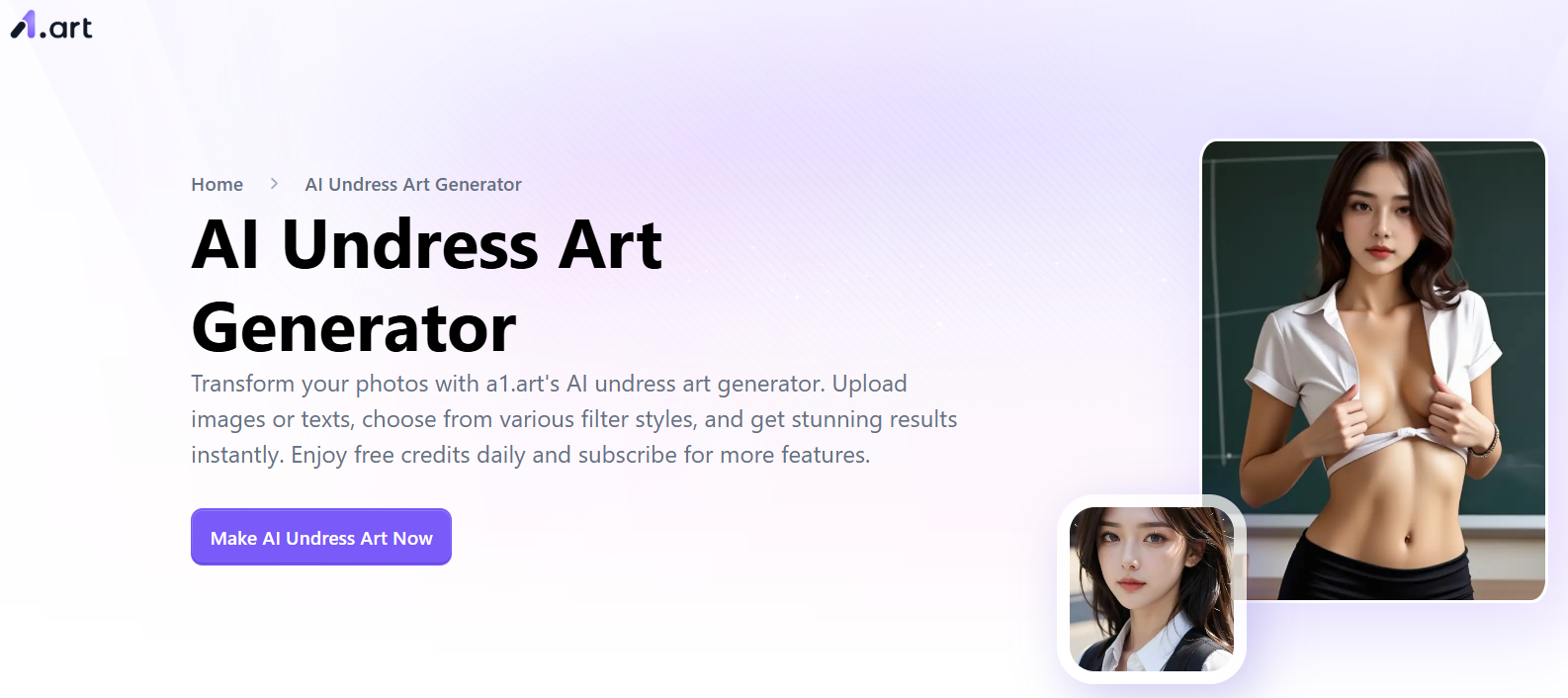
The market moved far beyond those early Deepnude software era. Today’s NSFW AI tools—often marketed as AI undress, AI Nude Builder, or virtual “AI girls”—promise realistic naked images from a single photo. Despite when their generation isn’t perfect, it remains convincing enough causing trigger panic, extortion, and social fallout. Across platforms, individuals encounter results through names like platforms such as N8ked, DrawNudes, UndressBaby, synthetic generators, Nudiva, and similar generators. The tools differ in speed, authenticity, and pricing, however the harm cycle is consistent: non-consensual imagery is created and spread more rapidly than most targets can respond.
Addressing this demands two parallel capabilities. First, develop to spot nine common red signals that betray AI manipulation. Second, maintain a response strategy that prioritizes documentation, fast reporting, along with safety. What follows is a actionable, experience-driven playbook utilized by moderators, trust and safety teams, and cyber forensics practitioners.
What makes NSFW deepfakes so dangerous today?
Accessibility, realism, and amplification combine to boost the risk assessment. The “undress application” category is remarkably simple, and online platforms can push a single fake to thousands among users before a takedown lands.
Low barriers is the central issue. A single selfie can become scraped from the profile and fed into a garment Removal Tool within minutes; some systems even automate groups. Quality is unpredictable, but extortion does not require photorealism—only believability and shock. Off-platform coordination in group chats and content dumps further grows reach, and several hosts sit beyond major jurisdictions. This result is one whiplash timeline: creation, threats (“send more or they nudivaapp.com post”), and circulation, often before any target knows how to ask for help. That renders detection and instant triage critical.
Red flag checklist: identifying AI-generated undress content
Most strip deepfakes share repeatable tells across physical features, physics, and context. You don’t need specialist tools; focus your eye on patterns that generators consistently get incorrect.
First, look for boundary artifacts and transition weirdness. Clothing boundaries, straps, and joints often leave ghost imprints, with flesh appearing unnaturally smooth where fabric might have compressed the surface. Jewelry, notably necklaces and adornments, may float, fuse into skin, and vanish between scenes of a brief clip. Tattoos along with scars are commonly missing, blurred, plus misaligned relative compared with original photos.
Second, scrutinize lighting, shadows, and reflections. Shadows under breasts or along the ribcage can appear artificially polished or inconsistent compared to the scene’s light direction. Reflections in mirrors, windows, and glossy surfaces may show original attire while the central subject appears naked, a high-signal discrepancy. Specular highlights on skin sometimes duplicate in tiled arrangements, a subtle generator fingerprint.
Third, check texture believability and hair movement. Skin pores might look uniformly artificial, with sudden quality changes around body torso. Body fur and fine strands around shoulders plus the neckline commonly blend into the background or show haloes. Strands that should overlap the body may become cut off, such legacy artifact within segmentation-heavy pipelines used by many strip generators.
Fourth, assess proportions plus continuity. Tan marks may be gone or painted artificially. Breast shape and gravity can contradict age and posture. Fingers pressing upon the body must deform skin; many fakes miss this micro-compression. Clothing traces—like a fabric edge—may imprint upon the “skin” through impossible ways.
Fifth, read the contextual context. Crops tend to avoid challenging areas such as underarms, hands on skin, or where clothing meets skin, concealing generator failures. Environmental logos or writing may warp, while EXIF metadata gets often stripped but shows editing software but not any claimed capture equipment. Reverse image checking regularly reveals source source photo with clothing on another platform.
Sixth, evaluate motion cues if it’s video. Breath doesn’t shift the torso; collar bone and rib motion lag the audio; and physics governing hair, necklaces, plus fabric don’t adjust to movement. Facial swaps sometimes close eyes at odd timing compared with typical human blink frequencies. Room acoustics plus voice resonance might mismatch the shown space if sound was generated or lifted.
Seventh, analyze duplicates and symmetry. AI loves mirrored elements, so you may spot repeated skin blemishes mirrored across the body, or identical wrinkles across sheets appearing across both sides across the frame. Background patterns sometimes mirror in unnatural blocks.
Eighth, look for account behavior red flags. Recently created profiles with minimal history that abruptly post NSFW “leaks,” aggressive DMs demanding payment, or confusing storylines about how a “friend” obtained the media signal predetermined playbook, not real circumstances.
Ninth, focus on consistency across a series. When multiple “images” showing the same individual show varying physical features—changing moles, disappearing piercings, or varying room details—the probability you’re dealing within an AI-generated group jumps.
What’s your immediate response plan when deepfakes are suspected?
Preserve evidence, keep calm, and work two tracks at once: removal along with containment. The first 60 minutes matters more compared to the perfect response.
Begin with documentation. Take full-page screenshots, the URL, timestamps, usernames, plus any IDs within the address location. Store original messages, covering threats, and film screen video showing show scrolling environment. Do not edit the files; store them in secure secure folder. When extortion is involved, do not send money and do not negotiate. Criminals typically escalate after payment because it confirms engagement.
Next, start platform and takedown removals. Report this content under “non-consensual intimate imagery” or “sexualized deepfake” when available. Send DMCA-style takedowns while the fake incorporates your likeness within a manipulated derivative of your image; many hosts accept these even when the claim is contested. Regarding ongoing protection, use a hashing service like StopNCII for create a unique identifier of your intimate images (or targeted images) so partner platforms can proactively block future posts.
Inform trusted contacts while the content affects your social group, employer, or school. A concise statement stating the content is fabricated while being addressed can blunt gossip-driven distribution. If the subject is a underage person, stop everything before involve law enforcement immediately; treat such content as emergency underage sexual abuse material handling and do not circulate such file further.
Finally, consider legal routes where applicable. Depending on jurisdiction, individuals may have grounds under intimate content abuse laws, false representation, harassment, defamation, and data protection. Some lawyer or local victim support agency can advise regarding urgent injunctions plus evidence standards.
Removal strategies: comparing major platform policies
Nearly all major platforms block non-consensual intimate content and synthetic porn, but policies and workflows vary. Act quickly and file on every surfaces where such content appears, covering mirrors and short-link hosts.
| Platform | Main policy area | Reporting location | Processing speed | Notes |
|---|---|---|---|---|
| Meta (Facebook/Instagram) | Non-consensual intimate imagery, sexualized deepfakes | In-app report + dedicated safety forms | Same day to a few days | Uses hash-based blocking systems |
| X social network | Unauthorized explicit material | Profile/report menu + policy form | Inconsistent timing, usually days | Requires escalation for edge cases |
| TikTok | Sexual exploitation and deepfakes | In-app report | Quick processing usually | Hashing used to block re-uploads post-removal |
| Non-consensual intimate media | Community and platform-wide options | Varies by subreddit; site 1–3 days | Pursue content and account actions together | |
| Smaller platforms/forums | Anti-harassment policies with variable adult content rules | Contact abuse teams via email/forms | Highly variable | Employ copyright notices and provider pressure |
Your legal options and protective measures
Current law is keeping up, and individuals likely have more options than you think. You don’t need to demonstrate who made this fake to demand removal under many regimes.
In the UK, sharing adult deepfakes without consent is a criminal offense under current Online Safety legislation 2023. In EU region EU, the AI Act requires labeling of AI-generated material in certain scenarios, and privacy legislation like GDPR enable takedowns where handling your likeness misses a legal basis. In the America, dozens of states criminalize non-consensual pornography, with several incorporating explicit deepfake provisions; civil claims for defamation, intrusion upon seclusion, or right of image rights often apply. Several countries also offer quick injunctive relief to curb distribution while a lawsuit proceeds.
If an undress picture was derived from your original image, copyright routes might help. A takedown notice targeting such derivative work plus the reposted source often leads into quicker compliance with hosts and indexing engines. Keep all notices factual, stop over-claiming, and mention the specific links.
Where platform enforcement stalls, escalate with follow-ups citing their stated bans on “AI-generated porn” and “non-consensual intimate imagery.” Persistence matters; repeated, well-documented reports outperform one vague request.
Personal protection strategies and security hardening
You won’t eliminate risk completely, but you can reduce exposure while increase your control if a problem starts. Think within terms of what can be extracted, how it could be remixed, along with how fast people can respond.
Harden your profiles through limiting public clear images, especially straight-on, well-lit selfies that undress tools favor. Consider subtle marking on public images and keep originals archived so you can prove origin when filing legal notices. Review friend networks and privacy options on platforms where strangers can message or scrape. Create up name-based alerts on search engines and social platforms to catch exposures early.
Build an evidence collection in advance: a template log for URLs, timestamps, along with usernames; a secure cloud folder; plus a short message you can provide to moderators outlining the deepfake. If individuals manage brand plus creator accounts, use C2PA Content Credentials for new uploads where supported when assert provenance. Regarding minors in individual care, lock up tagging, disable open DMs, and inform about sextortion scripts that start through “send a private pic.”
At work or academic settings, identify who deals with online safety issues and how fast they act. Establishing a response procedure reduces panic along with delays if anyone tries to circulate an AI-powered artificial nude” claiming the image shows you or a colleague.
Hidden truths: critical facts about AI-generated explicit content
Most deepfake content across platforms remains sexualized. Several independent studies from the past recent years found when the majority—often exceeding nine in every ten—of detected AI-generated media are pornographic and non-consensual, which corresponds with what websites and researchers observe during takedowns. Digital fingerprinting works without revealing your image openly: initiatives like blocking systems create a digital fingerprint locally and only share such hash, not the photo, to block additional posts across participating sites. EXIF metadata seldom helps once media is posted; leading platforms strip metadata on upload, thus don’t rely through metadata for authenticity. Content provenance protocols are gaining ground: C2PA-backed verification technology can embed signed edit history, enabling it easier to prove what’s authentic, but adoption is still uneven across consumer apps.
Quick response guide: detection and action steps
Pattern-match for the key tells: boundary anomalies, illumination mismatches, texture along with hair anomalies, dimensional errors, context mismatches, motion/voice mismatches, duplicated repeats, suspicious account behavior, and differences across a set. When you see two or multiple, treat it like likely manipulated before switch to action mode.
Capture evidence without redistributing the file extensively. Report on each host under unauthorized intimate imagery or sexualized deepfake policies. Use copyright plus privacy routes via parallel, and send a hash through a trusted prevention service where possible. Alert trusted people with a short, factual note when cut off distribution. If extortion or minors are present, escalate to criminal enforcement immediately and avoid any financial response or negotiation.
Beyond all, act quickly and methodically. Undress generators and online nude generators rely on shock plus speed; your benefit is a calm, documented process which triggers platform tools, legal hooks, along with social containment as a fake may define your reputation.
For clarity: references about brands like N8ked, DrawNudes, UndressBaby, AI nude platforms, Nudiva, and similar generators, and similar AI-powered undress app or Generator services remain included to describe risk patterns while do not recommend their use. This safest position stays simple—don’t engage with NSFW deepfake generation, and know methods to dismantle such content when it targets you or someone you care regarding.
